Most developers using AI coding tools like GitHub Copilot or Cursor think they’re just getting faster suggestions. But if you’re not using pattern libraries, you’re leaving security, consistency, and efficiency on the table. Pattern libraries aren’t fancy plugins or magic prompts-they’re structured, reusable templates that tell your AI assistant exactly how to write code for your project. And when used right, they cut bugs by more than half.
What Exactly Is a Pattern Library for AI?
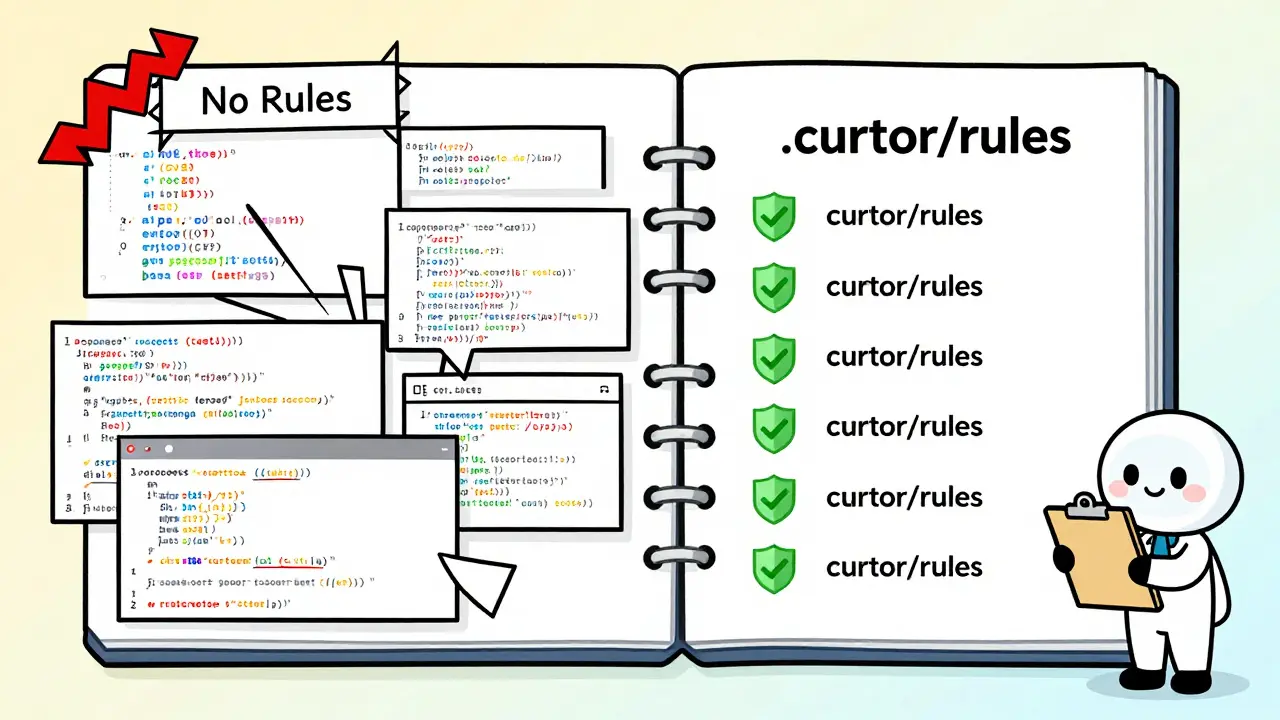
A pattern library for AI is a set of rules, templates, and conventions stored in your codebase that guide how AI tools generate code. Think of it like a style guide for your team-but instead of telling people to use camelCase or write comments, it tells AI tools: "Don’t use eval() in JavaScript," "Always validate user input in Flask," or "Use JWT tokens with a 15-minute expiry in this backend." These aren’t just tips. They’re machine-readable instructions. Most pattern libraries live in files like.cursor/rules/, AGENTS.md, or CLAUDE.md. They’re written in YAML or Markdown and loaded directly into AI coding assistants. When you ask the AI to "create a login endpoint," it doesn’t guess what you want-it checks your rules first.
This is the core of vibe coding: you’re not giving the AI a task and walking away. You’re having a conversation where the AI already knows your team’s rules, your stack, and your security limits. The result? Code that’s not just faster to write-but safer and more consistent from day one.
Why Vibe Coding Needs Pattern Libraries
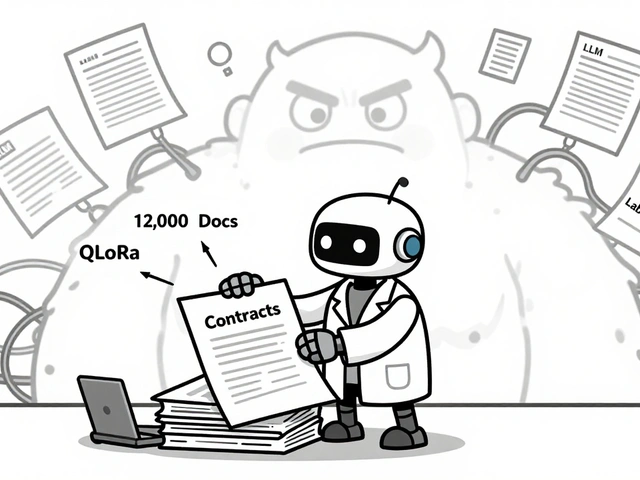
Vibe coding is different from traditional AI coding. In the old model, you’d say, "Write a function to calculate taxes," and the AI would generate something based on general knowledge. It might work. It might not. You’d have to fix it. In vibe coding, you say, "Add a new user registration route in our Django API," and the AI doesn’t just generate code-it generates code that matches your project’s exact structure, your team’s security policies, and your framework’s best practices. That’s because your pattern library told it how.Without pattern libraries, vibe coding turns into guesswork. A 2024 study by Wiz found that AI-generated code without rules had a 41% chance of including at least one high-severity vulnerability-things like SQL injection, missing authentication, or unvalidated file uploads. With pattern libraries, that number dropped to 15%.
And it’s not just security. Developers using structured rules reported 47% fewer code revisions. Why? Because the AI gets it right the first time. No more arguing over indentation, naming, or whether to use async/await or promises. Your rules enforce it.
How Pattern Libraries Actually Work
Pattern libraries work by layering constraints on top of the AI’s natural language understanding. Here’s how it breaks down:- Structure: Your rules define the project layout. For example: "All API routes go in
/api/, all models in/models/." - Context: The AI knows your tech stack: "This is a React + Node.js app using TypeScript, not Python."
- Action: It knows what to avoid: "Never use
eval(). Never hardcode secrets. Always use environment variables." - Format: It knows how to write: "Use Prettier settings from .prettierrc. Return JSON with camelCase keys. Use 2-space indentation."
- Feedback: The AI learns from past mistakes. If it generated a vulnerable endpoint last week, your rules remind it not to do it again.
Tools like Cursor and Wiz have taken this even further. Cursor’s rules system lets you assign severity levels: "Critical," "Warning," "Suggestion." You can block high-risk patterns outright, or just nudge the AI with gentle reminders. Wiz’s open-source rules for Django and Flask include specific checks for CWE-94 (Code Injection) and CWE-306 (Missing Authentication)-vulnerabilities that have plagued web apps for years.
Real-World Impact: Numbers That Matter
The data doesn’t lie. Here’s what teams are seeing after implementing pattern libraries:- 63% reduction in security vulnerabilities in AI-generated code (Wiz, 2024)
- 47% fewer code revisions (Graphite, May 2024)
- 32% faster feature delivery (Graphite, May 2024)
- 70% drop in critical security issues in a Flask API after applying Wiz’s Python rules (Reddit developer, May 2024)
- 62% fewer security-related PR comments at FinTech startup NovaPay after adopting the Vibe Coding Framework
But it’s not all wins. Some teams ran into problems. One developer on Stack Overflow said their rules were so strict that the AI started rejecting valid solutions-like using a slightly different library version that was still secure. Another team spent 2 hours converting GitHub Copilot instructions into Cursor rules when switching projects. That’s the cost of fragmentation.
Which Tools Support Pattern Libraries?
Not all AI coding tools are built the same. Here’s how the major players stack up:| Tool | Pattern Library Format | Security Enforcement | Framework-Specific Templates | Developer Rating (G2) |
|---|---|---|---|---|
| Cursor | .cursor/rules/ (YAML/Markdown) | High-severity levels, block rules | Yes-Python, JS, Java, .NET | 4.6/5 |
| GitHub Copilot | Repository Custom Instructions (plain text) | Low-no validation, no blocking | No | 3.9/5 |
| Cline | Custom Instructions (Markdown) | Moderate-basic constraints | Partial | 4.1/5 |
| Wiz (Open Source) | Rules files (YAML) | Very High-CVE/CWE mapped | Yes-Flask, Django, React, Spring | N/A (community-driven) |
| Graphite Agent | Codebase-aware rules | High-learns from history | Yes-context-aware | 4.7/5 |
Cursor and Graphite lead in enforcement. GitHub Copilot’s custom instructions are too vague-they’re like giving someone a list of "nice to haves" instead of rules. Wiz’s open-source rules are the gold standard for security, but they require manual setup. Graphite’s standout feature? It learns from your project’s history. If your team always uses a certain auth pattern, it remembers-not because you told it, but because it saw it in your code.
How to Start Using Pattern Libraries
You don’t need to rewrite your whole codebase. Start small:- Pick your stack: What frameworks are you using? Flask? React? Spring? Start with rules for those.
- Use Wiz’s open-source rules: Go to their GitHub repo. Download the rules for your framework. They’re free, battle-tested, and cover the top 5 vulnerabilities.
- Place them in the right folder: For Cursor, put them in
.cursor/rules/. For Cline, create aCLAUDE.mdfile in your root. - Test one feature: Ask the AI to build a new endpoint. See if it follows your rules. Fix any mismatches.
- Expand slowly: Don’t add 50 rules on day one. Start with 5 critical ones. Add more over time.
Wiz’s own data shows developers who start with comprehensive rules abandon them 3.7 times more often than those who start small. Build momentum, not complexity.
The Hidden Cost: Maintenance and Tool Lock-In
Pattern libraries aren’t set-and-forget. They need upkeep. When you upgrade Django from 4.2 to 5.0, does your rule still apply? When you switch from Cursor to Copilot, do your rules work the same way? They don’t.There’s a real risk of tool lock-in. Wiz’s rules are in YAML. Cursor uses its own format. GitHub Copilot uses plain text. If you build a library for one tool, you might have to rebuild it for another. That’s why many teams are starting to standardize on Markdown-based rules-they’re more portable.
Also, overly strict rules can backfire. One HealthTech developer reported their AI started rejecting valid code because the rules didn’t account for a legacy system they had to integrate with. The fix? Add exceptions. Rules aren’t laws-they’re guardrails. You should be able to override them when needed.
What Experts Are Saying
Dr. Elena Rodriguez from Wiz calls pattern libraries "the most practical near-term solution" to AI coding risks. She’s right. They fix known problems fast.But Dr. Marcus Chen from Google DeepMind warns: "They create a false sense of security." He’s also right. Rules can’t stop zero-day exploits or novel attack patterns. If your AI only knows what’s in your rules file, it won’t recognize a brand-new vulnerability that hasn’t been documented yet.
The consensus? Pattern libraries are necessary-but not sufficient. You still need static analysis tools, code reviews, and automated testing. Think of them as the first layer in a security onion, not the whole thing.
The Future: Where This Is Headed
By 2026, Gartner predicts 80% of enterprise AI coding tools will include built-in pattern library support. That’s not speculation-it’s already happening. Cursor launched a Rules Templates Marketplace with over 1,200 shared configurations in its first month. Wiz now auto-updates rules based on framework changelogs. And NIST’s AI Risk Management Framework now recommends pattern libraries as part of secure development.The market is growing fast. Forrester forecasts the AI code constraint tools market will hit $1.2 billion annually by 2027. That’s not because people want more AI-it’s because they want better, safer AI.
Final Thought: It’s Not About Speed. It’s About Trust.
The goal of vibe coding isn’t to write code faster. It’s to write code you can trust. Pattern libraries turn your AI from a helpful assistant into a reliable teammate. It doesn’t just follow your instructions-it follows your standards, your culture, your security policies.Start with one rule. Test it. Improve it. Share it. Soon, you won’t just be coding with AI. You’ll be coding with a team that already knows how you work.
What’s the difference between pattern libraries and AI coding prompts?
AI coding prompts are one-time instructions you type into a chat. Pattern libraries are reusable, stored-in-code templates that your AI assistant reads every time it generates code. Prompts are like giving someone directions for one trip. Pattern libraries are like giving them a GPS with saved home, work, and favorite routes.
Do I need to use a specific AI tool to benefit from pattern libraries?
No, but support varies. Cursor, Cline, and Graphite offer the strongest built-in support. GitHub Copilot’s Custom Instructions are basic and lack structure. You can use pattern libraries with any tool that lets you save text files in your project-but you’ll get the most benefit from tools designed for them.
Can pattern libraries prevent all security issues?
No. They prevent known, documented vulnerabilities-like SQL injection or missing auth-that have been codified into rules. But they can’t stop brand-new, unknown attacks (zero-days). Always pair pattern libraries with traditional security scanning tools and code reviews.
How long does it take to set up a pattern library?
You can get started in under an hour by downloading Wiz’s open-source rules for your framework. Building a full, custom library tailored to your team takes 8-12 hours of hands-on work. The key is starting small: pick 3-5 critical rules first, then expand.
Are pattern libraries only for security?
No. While security is the biggest driver, pattern libraries also enforce coding standards, framework conventions, API design patterns, and team workflows. They ensure everyone’s code looks and behaves the same way-no matter who writes it.
What happens if the AI ignores my rules?
Most tools will still generate code, but they’ll flag violations. Cursor, for example, shows warnings or blocks generation based on severity. If the AI keeps ignoring rules, check your file format, location, or syntax. Sometimes a typo in the YAML breaks the whole thing. Always test with a simple prompt first.

 Artificial Intelligence
Artificial Intelligence

Anand Pandit
January 10, 2026 AT 03:10I started using Wiz's Flask rules last month and wow-my team’s PR comments dropped by 60%. No more debates about whether to use JWT or sessions. The AI just knows. I didn’t even have to write a single rule myself-just downloaded, dropped into .cursor/rules/, and boom. It’s like having a senior dev whispering in the AI’s ear.
Reshma Jose
January 11, 2026 AT 05:40Guys I tried this with Copilot and it was a disaster. Custom instructions are useless-they’re like telling your dog to sit by whispering. But then I switched to Cursor and used the open-source Django rules? Changed everything. Code went from ‘meh, I’ll fix it later’ to ‘this is production-ready on first try’. Also, my manager noticed and asked if we hired a new dev. I told him it was just the rules.
rahul shrimali
January 12, 2026 AT 13:19Eka Prabha
January 13, 2026 AT 21:46Let’s be honest-this is just corporate AI-washing dressed up as ‘best practice’. You’re training your team to become code janitors who maintain brittle YAML files instead of actually learning the stack. And don’t get me started on tool lock-in. One vendor changes their format and suddenly your entire CI/CD pipeline is a graveyard of deprecated rules. This isn’t security-it’s vendor capture disguised as efficiency. The real solution? Hire competent engineers. Not more middleware.
Also, NIST recommending this? That’s like recommending duct tape as a primary structural reinforcement. You’re building a house out of Legos and calling it architecture.
Bharat Patel
January 14, 2026 AT 22:41There’s something beautiful about this-pattern libraries turn AI from a parrot into a conversation partner. It’s not about speed anymore. It’s about shared context. We used to think intelligence meant creativity. But maybe real intelligence is consistency. The ability to remember, adapt, and stay aligned without constant supervision. We’re not automating coding. We’re automating culture. And that’s scarier-and more powerful-than any prompt.
What if the future isn’t AI writing code for us… but AI helping us write the rules that define who we are as developers?